- Original Packed Sample: ae4d420c05281acf9696e558b02a42f8
- Unpacked Sample: f81064db46e305025ac6e2610e272eb3
- Source Url: hxxp://soksanhotels[.]com/calendar/daes/thai8.exe
- Info Url: URLhaus
- Automatic Generated Report: PepperMalware Report
- Virustotal First Submission: 2019-05-08 20:31:00
- Related links:
Analysis
- 1. About the Sample Classification
- 2. Loader
- 2.1. Shellcode and jump to unmanaged code
- 2.2. Hollow Process
- 3. Unpacked module
- 3.1. Strings Decryptor
- 3.1.1. Strings Index Mixer
- 3.1.2. AES Strings Encryption
- 3.1.2. List of Decrypted Strings
- 3.2. Decompiled Source Code With Decrypted Strings
- 4. Yara rules
1. About the Sample Classification
I have had lot of problems to classify this sample, not clear if Megalodon or Agenttesla SMTP variant.
At this tweet I tagged it as Agenttesla, and, in fact, when I started to write this article as agenttesla, then i changed to megalodon, and finally again to agenttesla.
I recomment these twitter threads, about this:
- https://twitter.com/dvk01uk/status/1082151041720897537
- https://twitter.com/P3pperP0tts/status/1127239398398013441
- https://twitter.com/avman1995/status/1072415443556679681
After reading this antiy labs analysis, I noticed the decrypted strings of the sample that I analyzed matched the strings of the sample analyzed by antiy labs.
It seems the sample that I analyzed is a newer version of the antiy labs article' one, with encryption of strings and a kind of mixer for the index into the table of encrypted strings.
2. Loader
2.1. Shellcode and jump to unmanaged code
The loader is not hardly obfuscated. The malware seems to decode a shellcode and a second unpacked PE from a image at resources:
Once the shellcode + pe is decrypted, it allocates memory (VirtualAlloc) and copies the shellcode there. To jump the unmanaged code (the shellcode) it creates a window and associates the shellcode address to that window (the window's procedure), and then it calls CallWindowProc:
2.2. Hollow Process
The shellcode creates a new suspended process from the same executable to perform hollow process:
In summary, the shellcode creates a new suspended process, calls NtUnmapViewOfSection to unmap the original PE image from memory, then allocates memory for writting the unpacked PE image (VirtualAllocEx), and copies the unpacked PE (mapping each section at the corresponding in memory rva) by calling WriteProcessMemory (btw, the injected PE is .Net PE, the unpacked agenttesla). Finally it calls SetThreadContext to set EIP = RtlUserThreadStart, and ResumeThread.
3. Unpacked Module
3.1. Strings Decryptor
The malware contains an array of encrypted strings (it is object_0 at this source):
Each time the malware needs a string, it calls a function that receives as argument an ID for the needed string:
3.1.1. Strings Index Mixer
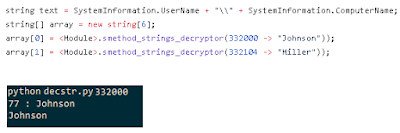
The string decryptor "smethod_strings_decryptor" doesn't receive a index into the array of encrypted strings as argument, it receives a kind of ID for the strings:
The first block of code of the decryptor of strings is a mixer (it is found in the same source that the encrypted strings) that transforms the given string ID to the index into the array of encrypted strings for that string:
An equivalent python code for this mixer is at github.
I guess this mixer could change between samples and versions.
3.2.2. AES Strings Encryption
Once an index into the array of encrypted strings is gotten, the string is decrypted. The format for each encrypted string in the array is:
[32 bytes AES key] [16 bytes AES IV][encrypted string]
And the string is decrypted by using AES_CBC algorithm. At github you can find an equivalent decryptor written in python:
https://github.com/p3pperp0tts/mlwcfg_tools/blob/master/AgentTesla_SMTP_Variant_05_2019/decstr.py
It receives as argument an string ID and print the decrypted string for that ID.
3.2.3. List of Decrypted Strings
Here it's the full list of decrypted strings that the analyzed sample use:
https://github.com/p3pperp0tts/mlwcfg_tools/blob/master/AgentTesla_SMTP_Variant_05_2019/encstr.txt
3.2. Decompiled Source Code With Decrypted Strings
I have uploaded a decompiled source code for the unpacked agenttesla from sample ae4d420c05281acf9696e558b02a42f8:
This source code is commented with the associated decrypted string for each part of the code where an string is being decrypted, making easier to understand the malware behavior:
4. Yara Rules
Yara Rule for Unpacked AgentTesla:
From this code:
rule AgentTesla_SMTP_Variant_05_2019_mem {
strings:
$AESdec = { 28 ?? ?? ?? ?? 25 FE 09 01 00 6F ?? ?? ?? ?? 25 FE 09 02 00 6F ?? ?? ?? ?? 6F ?? ?? ?? ?? FE 09 00 00 20 00 00 00 00 FE 09 00 00 8E 69 6F ?? ?? ?? ?? 2A }
$StrDecLast = { 25 16 07 16 09 28 ?? ?? ?? ?? 25 09 08 16 11 04 28 ?? ?? ?? ?? 09 11 04 58 11 0D 16 11 0C 28 ?? ?? ?? ?? 28 ?? ?? ?? ?? 11 0D 07 08 28 ?? ?? ?? ?? 6F ?? ?? ?? ?? 2A }
condition:
all of them
}
From this code:










No comments:
Post a Comment